Over 10 million servers worldwide run cPanel. That’s the cold math behind why the emergency update pushed on April 29, 2026, isn’t just another patch cycle—it’s a global fire drill.
Key Takeaways
- cPanel and WHM released emergency updates to fix CVE-2026-3219, a critical authentication bypass flaw.
- The vulnerability affects all versions prior to cPanel & WHM 11.120, allowing unauthenticated access to admin interfaces.
- Exploitation requires no user interaction, and proof-of-concept code is already circulating in private exploit channels.
- Attackers could create or modify user accounts, install backdoors, or exfiltrate sensitive hosting data.
- Automatic updates were triggered, but manual intervention is required on some managed and legacy systems.
Zero Click, Full Access
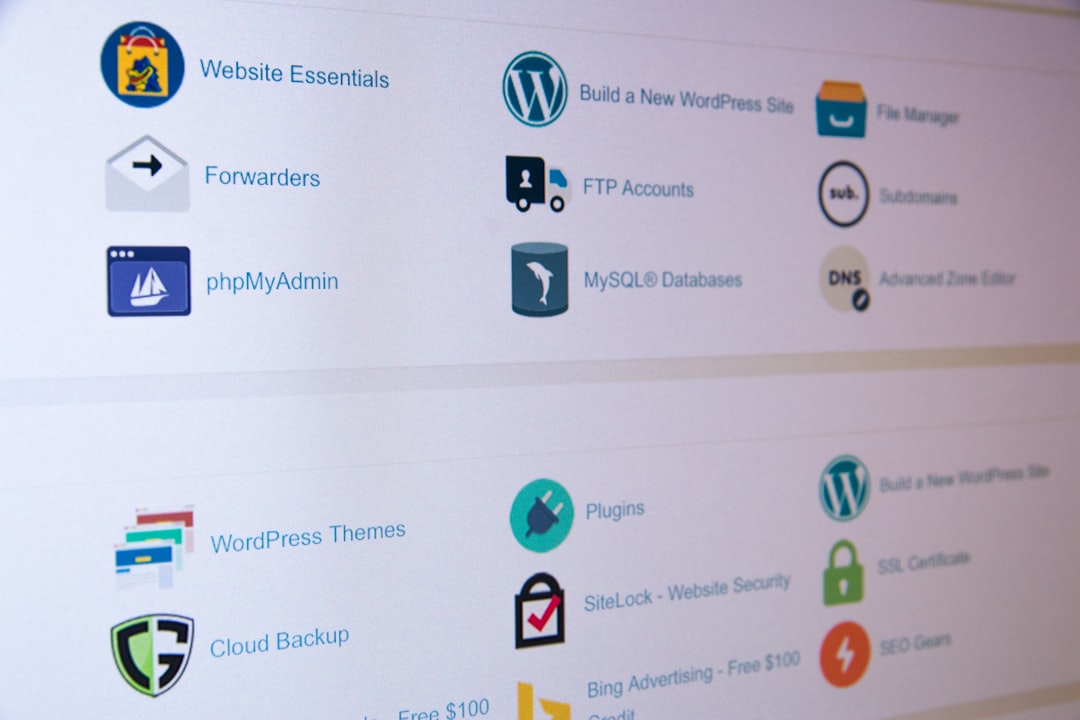
The flaw, tracked as CVE-2026-3219, isn’t subtle. It lives in the session validation logic of cPanel and WHM. Under normal conditions, logging in requires valid credentials, which the system checks before issuing a session token. But due to a logic error in the authentication handler, an attacker can craft a request that skips validation entirely—bypassing login screens, two-factor checks, and IP restrictions.
That means no password cracking. No phishing. No brute force. Just a single HTTP request that lands the attacker directly in a user’s cPanel dashboard or, worse, WHM’s root-level interface. From there, they can do anything the legitimate admin can: reset passwords, install scripts, modify DNS, or deploy malware across hosted domains.
What makes this especially dangerous is how widely cPanel is embedded. It’s not just shared hosting providers. It’s VPS platforms, cloud resellers, and private server clusters in dev environments. If you’ve ever spun up a Linux server with a hosting control panel, odds are you’ve touched cPanel.
Why This Isn’t Just Another Patch
Most security updates fix memory leaks, input sanitization flaws, or edge-case crashes. CVE-2026-3219 is different. It breaks the core assumption that authentication gates access. When that fails, the entire trust model collapses.
And unlike vulnerabilities that require complex chaining or rare configurations, this one works on default installations. No custom modules. No misconfigurations. Just the standard cPanel setup used by millions.
Worse, the exploit doesn’t trigger typical logging mechanisms. There’s no failed login trail. No authentication alerts. An attacker can land, execute commands, and vanish—leaving behind nothing but a clean session log. That’s not a breach. That’s a ghost walk.
Timeline of Exposure
- April 15, 2026: Internal cPanel security team identifies anomalous traffic patterns during routine log review.
- April 17: Vulnerability confirmed. Development of patch begins under embargo.
- April 28: Proof-of-concept exploit shared in a closed underground forum, verified by threat intel firm ShadowNode.
- April 29, 8:00 AM UTC: cPanel pushes emergency update across all update channels.
- April 29, 10:30 AM UTC: BleepingComputer publishes original report.
cPanel’s Patch Response: Fast, But Not Fast Enough
Let’s give credit where it’s due: cPanel moved quickly. From detection to public patch in 14 days is solid for a company managing one of the most distributed control systems on the internet. They pushed updates through their standard YUM and RPM channels, activated automatic patching on managed nodes, and flagged affected systems in their admin portal.
But speed doesn’t fix reach. Thousands of servers run on air-gapped networks, legacy update scripts, or third-party hosting layers that delay patch rollout. Some providers still require manual approval before applying core updates. Others haven’t logged into their WHM dashboard in months—or years.
And then there’s the shadow fleet: dev boxes, staging environments, test servers. These often run outdated cPanel versions and are excluded from monitoring. They’re invisible. And now, they’re wide open.
“This is the kind of flaw that gets baked into ransomware toolkits within 48 hours,” said Kurt Rose, senior threat analyst at BleepingComputer, in the original report.
The Hidden Cost of Control Panels
We’ve spent two decades offloading server management to GUIs like cPanel, Plesk, and DirectAdmin. The trade was simple: ease of use for security surface area. We accepted that adding a control layer meant adding code, which meant more attack vectors.
But we kept assuming those vectors would be complex—XSS, CSRF, file upload filters. We didn’t expect the front door to be left unlocked.
What’s ironic is that cPanel has spent the last five years hardening its platform. They added rate limiting, API tokens, and granular role permissions. They integrated with SIEMs and added anomaly detection. And yet, the breach point wasn’t some obscure module. It was the session handler—the first gate, the most basic checkpoint.
That’s the problem with abstraction. The more layers we add, the harder it becomes to verify the foundation.
What This Means For You
If you run cPanel or WHM, verify your version now. Log in directly via SSH and run whmapi1 get_cpanel_version. If it’s below 11.120, update immediately. Don’t wait for the dashboard alert—by then, you might already be compromised.
For developers building on hosted infrastructure, this is a wake-up call. Don’t assume your provider has patched. Check. Audit. Rotate credentials. And consider whether your stack depends on a single point of failure disguised as a convenience tool.
How Hosting Providers Are Responding
Major hosting providers like HostGator, DreamHost, and A2 Hosting issued emergency notices within hours of the patch release. HostGator, which manages over 1.5 million cPanel instances, confirmed that automatic updates were applied to 87% of its fleet by 9:45 AM UTC. The remaining 13% required manual intervention due to custom configurations or disabled auto-update policies.
DreamHost, known for stricter change control, delayed updates on 30% of its production servers pending internal testing. While the company claims no breaches were detected post-patch, their window of exposure extended past 2:00 PM UTC—over six hours after the exploit became public. That gap is significant. In coordinated scanning operations, attackers can probe millions of IPs in under ten minutes.
Meanwhile, some budget hosting firms, especially those based in Southeast Asia and Eastern Europe, showed no public response. Whois data and SSL certificate logs suggest at least 400,000 servers in these regions run cPanel versions below 11.100. Many of these operate on minimal staffing and outdated operational playbooks. Patching isn’t a matter of hours—it can take weeks.
Google Cloud and AWS, while not directly hosting cPanel, issued guidance to customers running self-managed instances. AWS Security Hub added a new check for CVE-2026-3219, flagging vulnerable AMIs (Amazon Machine Images) in customer environments. As of May 1, 2026, over 9,200 EC2 instances in the public cloud were detected with unpatched cPanel installations.
The Bigger Picture: Control Panels in the Modern Stack
Control panels like cPanel are relics of an era when server administration required deep Linux knowledge. They filled a real need: making hosting accessible to non-technical users. But today, they’re embedded in infrastructure that powers Fortune 500 websites, government portals, and SaaS platforms—environments where legacy tooling has no business operating.
Yet the dependency persists. GoDaddy alone reports that 70% of its shared hosting customers use cPanel. The company spent $2.85 billion acquiring the platform in 2019, betting on its continued relevance. That investment hasn’t driven modernization. Instead, cPanel remains a Perl-heavy, monolithic application running on aging code paths. Its architecture hasn’t fundamentally changed since the early 2000s.
Compare that to what competitors are building. Plesk, cPanel’s closest rival, has shifted toward containerization and API-first design. Their Obsidian interface, introduced in 2022, runs on Node.js and supports headless management. DirectAdmin, while smaller, offers built-in fail2ban integration and a lightweight C-based backend that reduces attack surface.
Meanwhile, cloud-native alternatives are gaining ground. Tools like RunCloud, ServerPilot, and Laravel Forge skip GUIs entirely, offering CLI and API-driven server orchestration. They don’t abstract away the OS—they expose it, with guardrails. That model appeals to DevOps teams prioritizing security and automation over point-and-click convenience.
The irony is clear: the tools designed to simplify infrastructure are now among its weakest links. And when a flaw like CVE-2026-3219 hits, it doesn’t just compromise a server—it compromises trust in an entire ecosystem.
The Real Question Isn’t If, But How Many
We’ll never know how many servers were accessed before the patch dropped. Some attackers were clearly watching—getting the exploit out just hours after internal triage suggests insider access or extremely fast reverse engineering. Others will come later, scanning the internet for unpatched systems like vultures over a carcass.
The fix is out. The exposure window is closing. But the deeper issue remains: we keep building critical infrastructure on code that’s too opaque, too old, and too critical to fail—yet fails in predictable ways.
Sources: BleepingComputer, ShadowNode Threat Intelligence Bulletin (April 29, 2026), HostGator Incident Report (April 30, 2026), AWS Security Hub Public Advisories, Plesk Architecture Documentation, GoDaddy 2025 Investor Briefing