The DAEMON Tools software, a popular tool for creating and managing virtual drives, has been compromised through a supply chain attack. According to Kaspersky researchers, the attack occurred through the software’s official installers, which were distributed from the legitimate website of DAEMON Tools. These installers were signed with digital certificates belonging to DAEMON Tools developers, making them appear legitimate.
Key Takeaways
- The DAEMON Tools software has been compromised through a supply chain attack.
- The attack occurred through the software’s official installers, which were distributed from the legitimate website.
- The installers were signed with digital certificates belonging to DAEMON Tools developers.
- The compromise was discovered by Kaspersky researchers.
- The attack has compromised the official installers of DAEMON Tools software with malware.
The Attack Details
These installers were distributed from the legitimate website of DAEMON Tools and were signed with digital certificates belonging to DAEMON Tools developers. This made them appear legitimate and trustworthy to users. However, Kaspersky researchers discovered that these installers contained a malicious payload that compromised the users’ systems.
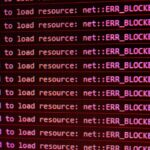
The malware wasn’t injected into the core application itself but embedded within the installer package—specifically, during the bundling phase before public release. That means every user who downloaded DAEMON Tools from the official site during the active period of the compromise likely installed malware alongside the intended software. The payload communicates with a remote command-and-control server shortly after installation, potentially enabling attackers to exfiltrate data, install additional tools, or move laterally across networks.
Because the binaries were properly signed with valid certificates issued to the real development team, antivirus solutions and OS-level trust mechanisms did not flag the downloads as suspicious. This level of legitimacy is what makes supply chain attacks so effective—and so hard to detect. Kaspersky noted that the malicious code was carefully obfuscated, using techniques that delay execution and hide network traffic to avoid sandbox detection in security software.
What sets this incident apart from typical malware distribution campaigns is the precision and access required. The attackers didn’t exploit a third-party updater or a compromised ad network. They infiltrated the actual build or distribution infrastructure of DAEMON Tools. That suggests either a breach of developer credentials, unauthorized access to build servers, or a compromise of the signing process itself.
It’s unclear how long the compromised installers were live on the site, but Kaspersky’s telemetry indicates downloads spiked in late April, with sustained activity through early May. The company has not yet confirmed when the malicious binaries were first deployed, though analysis of version timestamps suggests the earliest tainted builds may have been released at least two weeks before detection.
The Impact
The impact of this attack is significant, as it compromises the security of users who have installed the DAEMON Tools software. This can lead to various security threats, including Data Breaches, ransomware attacks, and other malicious activities. The compromise of the official installers also raises concerns about the security of the software development process.
DAEMON Tools has millions of users worldwide, including individuals, IT professionals, and even enterprise environments where virtual drive software is used for testing or legacy application support. While the exact number of affected users isn’t known, the fact that the malware was distributed via the primary download channel means exposure could be broad.
In corporate settings, the implications are especially serious. A single infected workstation could serve as an entry point for attackers to pivot into internal systems. Given that DAEMON Tools often requires elevated privileges to function—particularly when mounting images or emulating hardware—the malware may have gained high-level access right from installation.
Beyond immediate system compromise, the breach undermines trust in digital signatures. For years, developers and organizations have relied on code signing as a gold standard for verifying software integrity. When a signed installer turns malicious, it calls into question whether any binary can be trusted—even those from reputable sources.
There’s also reputational damage. DAEMON Tools has been around since the early 2000s and built a reputation for reliability. This incident could erode user confidence, especially among more security-conscious audiences. It may take months, if not years, to rebuild trust, particularly if forensic analysis reveals deeper systemic flaws in their development pipeline.
The Investigation
Kaspersky researchers are currently investigating the attack and have discovered that the malicious payload was downloaded from the official website of DAEMON Tools. The researchers are working to determine the extent of the compromise and to identify the attackers behind the attack.
So far, the investigation has focused on reverse-engineering the payload, mapping its communication patterns, and identifying indicators of compromise (IOCs). Kaspersky has shared hashes of the malicious installers and domains used for C2 with other security vendors and industry threat-sharing groups.
One critical question investigators are trying to answer is whether the attackers still have access to DAEMON Tools’ infrastructure. If the initial breach hasn’t been fully contained, there’s a risk of follow-up attacks or continued data exfiltration. Kaspersky has urged DAEMON Tools to conduct a full audit of their development, build, and release pipelines—including access logs, key management, and third-party dependencies.
Another line of inquiry involves the digital certificates used to sign the malware. Were they stolen? Were they misused by an insider? Or was the signing process itself hijacked? Certificate revocation is one response, but it doesn’t explain how the breach occurred in the first place. Reissuing certificates without fixing underlying vulnerabilities only delays the next incident.
At this stage, no attribution has been made. The tactics, techniques, and procedures (TTPs) observed don’t clearly point to any known threat actor. There’s no ransomware deployment, no immediate data theft, and no geopolitical pattern in victim locations. That could mean the attackers are still in the reconnaissance phase—or that this was a financially motivated campaign aiming for stealth and persistence rather than disruption.
What This Means For You
This attack highlights the importance of verifying the authenticity of software installers before installing them. Users should be cautious when downloading software from the internet and should only download installers from trusted sources. Users should ensure that their systems are up-to-date with the latest security patches and updates.
But in practice, “trusted sources” are harder to define than they used to be. The DAEMON Tools site *is* the trusted source—yet it hosted malware. So what should users actually do?
For developers and software teams, this incident is a wake-up call. If you maintain open-source or commercial software, you must assume your build pipeline is a target. Implement strict access controls. Rotate signing keys regularly. Use hardware security modules (HSMs) for code signing, so private keys never leave secure devices. Monitor for unusual activity—like unexpected builds or large data transfers from build servers.
For startup founders relying on third-party tools to run their infrastructure, this is a reminder to limit software privileges. Just because an app needs admin rights doesn’t mean every employee should install it with them. Enforce application whitelisting where possible, and use endpoint detection and response (EDR) tools to catch suspicious behavior post-install.
For enterprise IT teams, this reinforces the need for layered defense. Assume that some endpoints will get compromised. Segment your network so one infected machine can’t access sensitive databases or domain controllers. Conduct regular audits of installed software, especially utilities like DAEMON Tools that might fly under the radar.
And for everyday users? Don’t skip checksum verification. Many software vendors publish SHA-256 hashes on their sites. Compare the hash of your downloaded file with the one on the official page. It takes seconds and can stop a lot of trouble. Also, consider whether you even need the software. DAEMON Tools is useful, but how often do you really use it? The fewer programs you install, the smaller your attack surface.
Competitive Landscape and Industry Precedents
This isn’t the first time a widely used utility has been weaponized through its own distribution channel. In 2020, the popular CCleaner software was compromised in a similar supply chain attack, where attackers replaced legitimate installers with backdoored versions. That breach affected millions and led to follow-on attacks against major tech firms.
Earlier, in 2017, the NotPetya attack spread via a compromised update to the Ukrainian accounting software MeDoc. That single breach cascaded into global chaos, hitting multinational corporations and causing billions in damages.
More recently, the SolarWinds Orion breach in 2020 showed how devastating a well-executed supply chain compromise can be. Attackers inserted malicious code into legitimate software updates, giving them access to U.S. government agencies and Fortune 500 companies.
What these incidents have in common is trust exploitation. Attackers don’t try to trick users into downloading fake software—they let users download the real thing, poisoned from within. DAEMON Tools now joins that list, not because it’s uniquely vulnerable, but because it’s popular, trusted, and likely underestimated as a target.
Smaller software vendors often lack the resources for strong security infrastructure. They may not employ full-time security staff, use multi-factor authentication on build systems, or conduct regular penetration tests. Yet their software is installed on high-value machines. That makes them perfect stepping stones for attackers aiming at bigger targets.
The DAEMON Tools case also highlights a gap in how users perceive risk. Tools for mounting ISOs or emulating drives are often seen as low-risk utilities. They’re not handling passwords or financial data, so they fly under the radar. But any software that runs with system privileges and connects to the internet becomes a potential attack vector.
Key Questions Remaining
Despite Kaspersky’s findings, several critical questions remain unanswered.
Was the breach limited to the installer, or did the attackers modify the Source Code repository itself? If the source was altered, then even clean rebuilds might carry hidden backdoors.
How did the attackers gain access? Was it a phishing attack on a developer? A misconfigured server? A third-party vendor with access to the build system?
Have all compromised certificates been revoked and replaced? If not, attackers could sign new malware and distribute it under the DAEMON Tools name long after the initial fix.
And perhaps most importantly—how many systems are already infected? The malware’s ability to phone home suggests ongoing communication with attacker infrastructure. Even if clean installers are now available, the window of exposure might have been wide enough to allow sustained access in some environments.
We also don’t know if DAEMON Tools has notified law enforcement or regulatory bodies. Depending on where their users are based, data breach notification laws may require disclosure, especially if personal or corporate data was accessed.
Until these questions are answered, users and organizations should treat all past downloads of DAEMON Tools with suspicion. Consider uninstalling the software unless absolutely necessary. Scan systems for known IOCs. And monitor network traffic for signs of beaconing to suspicious domains.
It’s concerning to see a well-established software like DAEMON Tools fall victim to a supply chain attack. This attack serves as a reminder of the importance of strong security measures in software development and distribution.
The Future of Software Security
As software becomes increasingly complex and interconnected, the threat of supply chain attacks will only continue to grow. It’s essential for software developers and distributors to prioritize security and implement strong measures to prevent such attacks. This may include implementing secure coding practices, conducting thorough security audits, and verifying the authenticity of software installers.
The DAEMON Tools incident isn’t an anomaly—it’s a signal. The tools we depend on are only as secure as the weakest link in their creation chain. And for too long, that chain has been built on assumptions: that internal networks are safe, that signing equals trust, that small dev teams don’t need enterprise-grade security.
That mindset has to change. Software vendors, no matter their size, must treat their build and release pipelines as crown jewels. Attackers know that. They’re not always going after the front door—they’re looking for the delivery entrance in the back.
As we look to the future, it’s clear that software security will continue to be a pressing concern. The DAEMON Tools supply chain attack is a stark reminder of the need for vigilance and proactive security measures in the software industry.
Sources: The Hacker News, Kaspersky